Laptop Virus Enccrypted Files Blue Screen Pc Needs Repair
Home > Ransomware > .corrupt Files Virus – How to Remove and Restore Encrypted Documents
Threat Summary .corrupt Ransomware – Spreading Methods.corrupt Ransomware Virus – ActivityHow Does .corrupt Ransomware EncryptRemove .corrupt Files Virus and Recover Encrypted Documents
 This article has a goal to help you by showing you how to remove the .corrupt file extension ransomware virus from your computer and explain how to restore files that have been encrypted by it without having to pay ransom.
This article has a goal to help you by showing you how to remove the .corrupt file extension ransomware virus from your computer and explain how to restore files that have been encrypted by it without having to pay ransom.
New form of ransomware infection, appending the .corrupt file extension after it encrypts the files on the infected computer has been reported by victims. The malware aims to make the important documents on the computers infected by it no longer able to be opened and after this, the virus also aims to get the victim to pay a hefty ransom fee in order to make his files usable again. The virus may demand different cryptocurrencies as a form of payment, primarily BitCoin. If you have been infected by the .corrupt files ransomware, paying the ransom is highly inadvisable and we recommend you to read the following article in order to learn how to remove this ransomware infection and try to recover files encrypted with .corrupt file extension added to them without paying to cyber-criminals.

Threat Summary
| Name | .corrupt Ransomware |
| Type | Ransomware, Cryptovirus |
| Short Description | A virus from the file encryption type. Encrypts the files on your computer, and then asks you to contact a random-named ProtonMail e-mail account for further demands. |
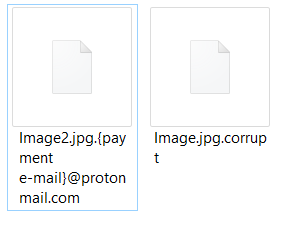
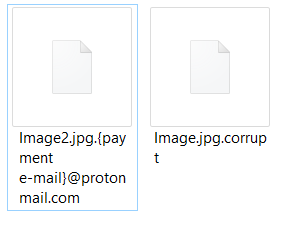
| Symptoms | Appends two file extensions to the encrypted files – .corrupt and a random-named e-mail address for payment. |
| Distribution Method | Spam Emails, Email Attachments, Executable files |
| Detection Tool | See If Your System Has Been Affected by malware Download Malware Removal Tool |
| User Experience | Join Our Forum to Discuss .corrupt Ransomware. |
| Data Recovery Tool | Windows Data Recovery by Stellar Phoenix Notice! This product scans your drive sectors to recover lost files and it may not recover 100% of the encrypted files, but only few of them, depending on the situation and whether or not you have reformatted your drive. |

.corrupt Ransomware – Spreading Methods
In order to get this ransomware out there and running, the cyber-criminals have though the process through. They may have utilized an exploit kit which uses vulnerabilities in unpatched Windows systems to enter undetected and drop the malicious files of the ransomware via an intermediary infection file or a malicious web link. These objects are often seen as fake e-mail attachments, like the one in the malicious e-mail that is carefully disguised below:
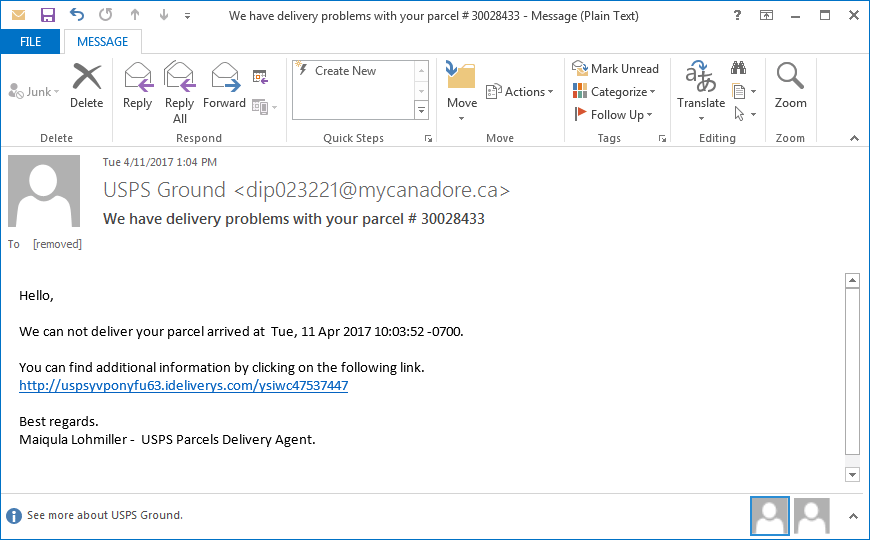
After the victim opens the malicious file, the infection process is triggered and the malicious file drops the payload of the virus on the victim's computer. Usually, the file may be obfuscated itself in order to avoid conventional antivirus programs from detecting it. This process ensures a more successful infection to take place.
In addition to via e-mail, the ransomware may infect users via multiple different types of files that may pose as legitimate ones, for instance:
- Software setups.
- License activators.
- Game patches and game cracks.
- Fake torrent files.

.corrupt Ransomware Virus – Activity
Once the payload of the .corrupt files virus is dropped, it may consist of more than one malicious files and these files may reside in the following commonly targeted Windows directories:
- %AppData%
- %Local%
- %Roaming%
- %LocalLow%
- %Temp%
After having dropped it's malicious files, the .corrupt files virus may perform other activities on the computer of the victims, like interfere with the following Run and RunOnce Windows registry sub-keys by adding registry value strings with data in them:
→ HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
This allows for the .corrupt files virus to run it's malicious files automatically when Windows starts up. If you check the data of those registry entries, which are usually value strings with random names, the actual file encrypting executable's location can be discovered.
In addition to this, the .corrupt files virus also obtains permissions to run administrative commands via the Windows Command Prompt. Some of the commands which the virus may run on your computer may be hidden from your sight and delete your backups, shadow volume copies plus disable the Windows Recovery service. The commands are usually ran via a script and are the following:
→ process call create "cmd.exe /c vssadmin.exe delete shadows /all /quiet & bcdedit.exe /set {default} recoveryenabled no & bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures"

How Does .corrupt Ransomware Encrypt
To perform the encryption process of the infected computer, the .corrupt files virus may begin to scan the infected machine for the following types of files:
- Documents.
- Videos.
- Music files.
- Archives.
- Virtual drive files (.vdmk, etc.).
The encryption process may be performed by using the AES or RSA encryption algorithms (or both in combination) via different encryption modes, like RC4 for example. This is done with the purpose of increasing the difficulty to decipher the decryption key which is generated after the process is complete. The files no longer look the same and appear with one of the following file extensions:

Remove .corrupt Files Virus and Recover Encrypted Documents
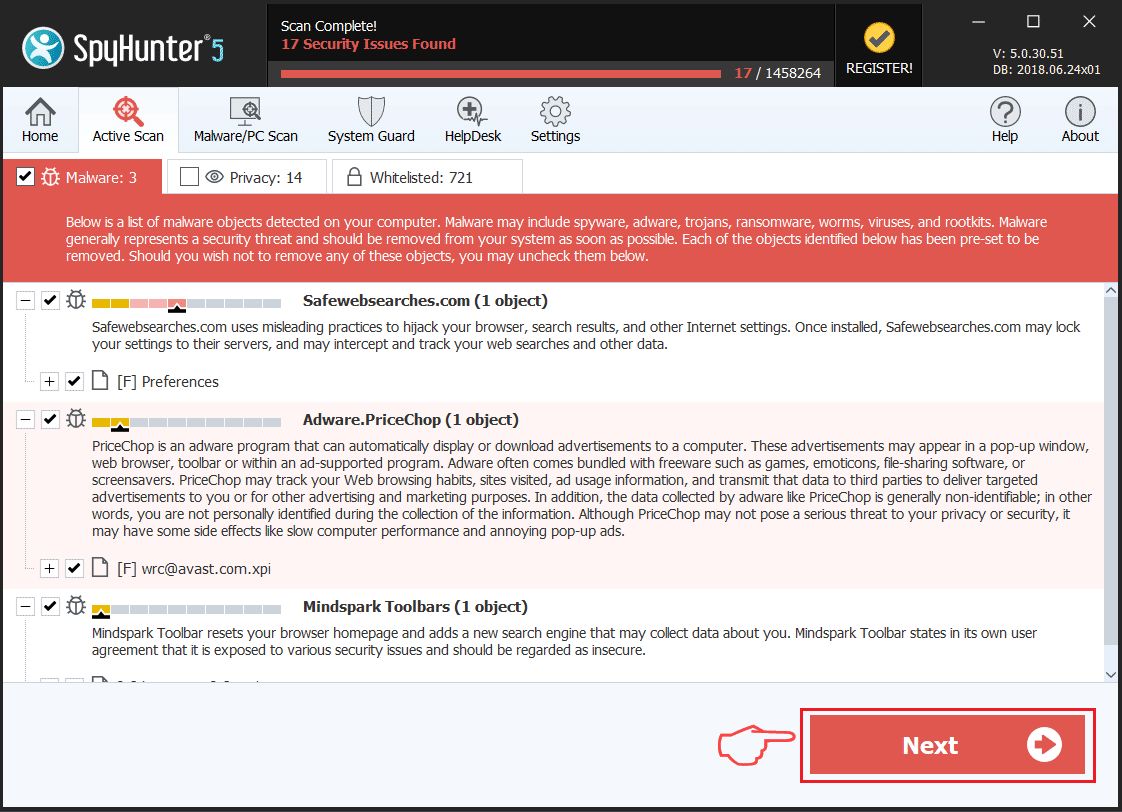
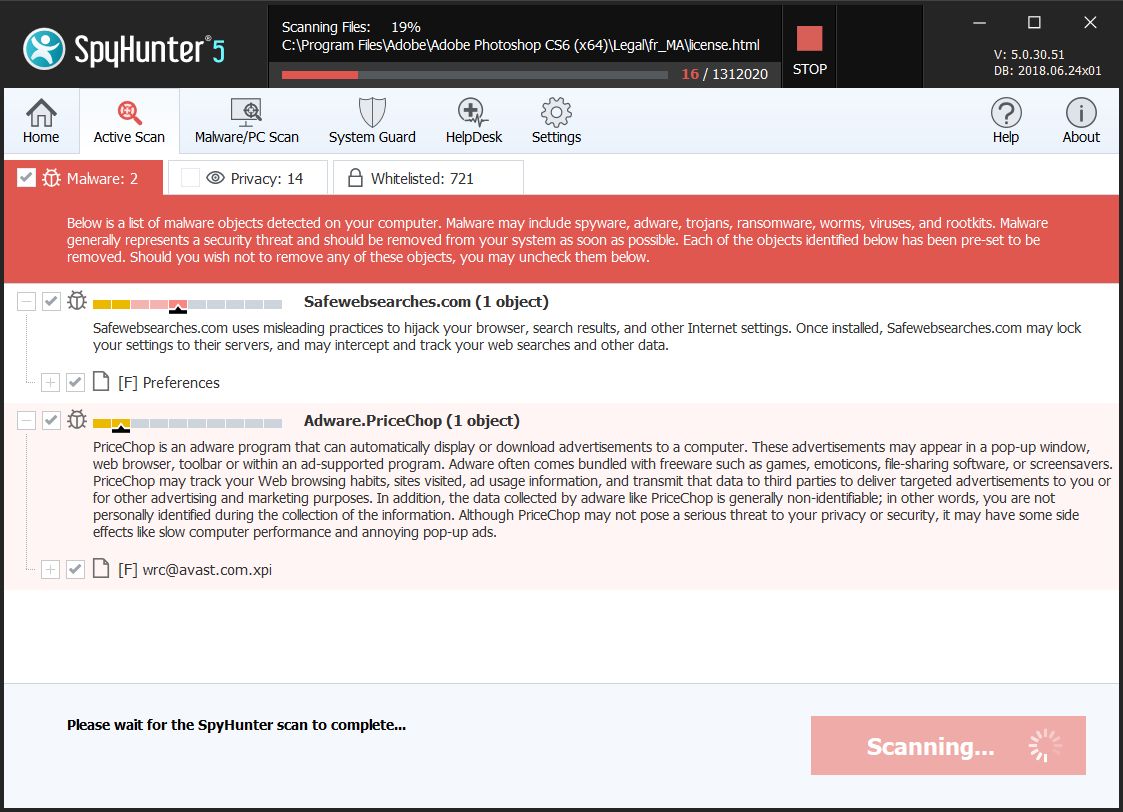
In order to remove this ransomware infection from your computer, you will need to have some experience. The preferred methods to do the removal are via following the manual or the automatic removal instructions below. If you lack the experience in manual removal, security experts strongly advise downloading and scanning your computer with an advanced anti-malware scanner, which will automatically delete all of the objects, related ot the .corrupt files virus and protect your computer against future threats.
In order to try and restore as many files as you can, you can try the alternative file recovery methods which we have suggested from step "2. Restore files encrypted by .corrupt Ransomware" below. The methods may not be 100% effective, but can help recover multiple files that have been encrypted without you having to pay for decryption to the cyber-criminals.
Attention! SensorsTechForum strongly recommends that all malware victims should look for assistance only by reputable sources. Many guides out there claim to offer free recovery and decryption for files encrypted by ransomware viruses. Be advised that some of them may only be after your money.
As a site that has been dedicated to providing free removal instructions for ransomware and malware since 2014, SensorsTechForum's recommendation is to only pay attention to trustworthy sources.
How to recognize trustworthy sources:
- Guide 1: How to Remove .corrupt Ransomware from Windows.
- Guide 2: Get rid of .corrupt Ransomware from Mac OS X.
Windows Mac OS X
How to Remove .corrupt Ransomware from Windows.
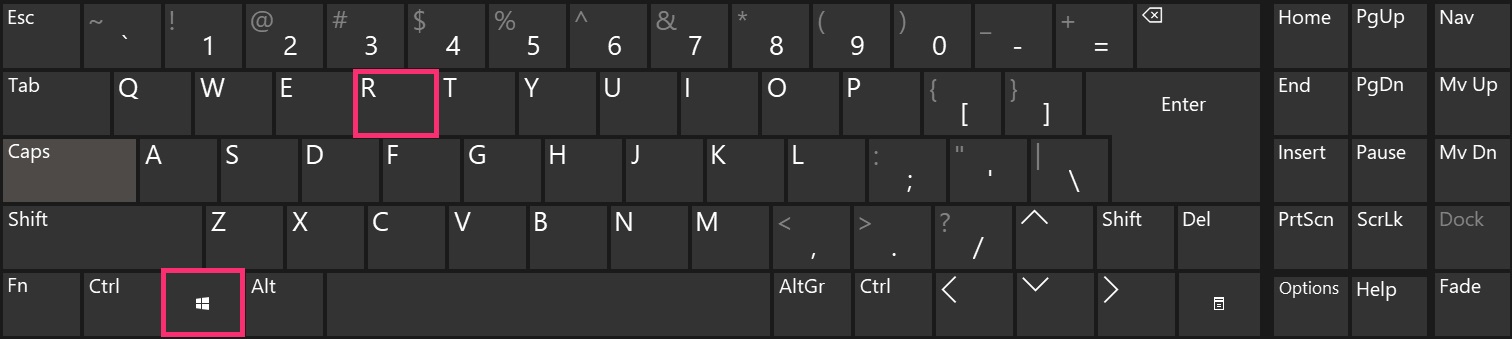
Step 1: Boot Your PC In Safe Mode to isolate and remove .corrupt Ransomware
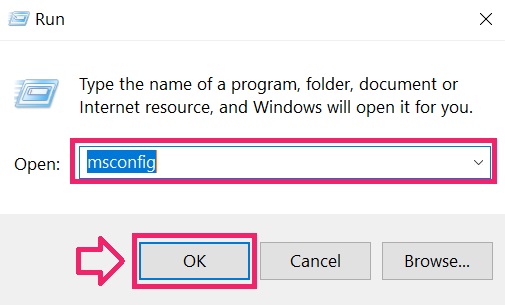

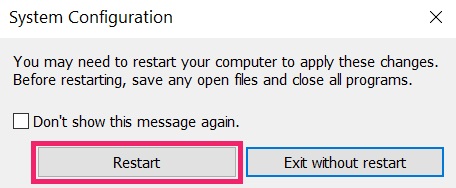

Step 2: Uninstall .corrupt Ransomware and related software from Windows
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:

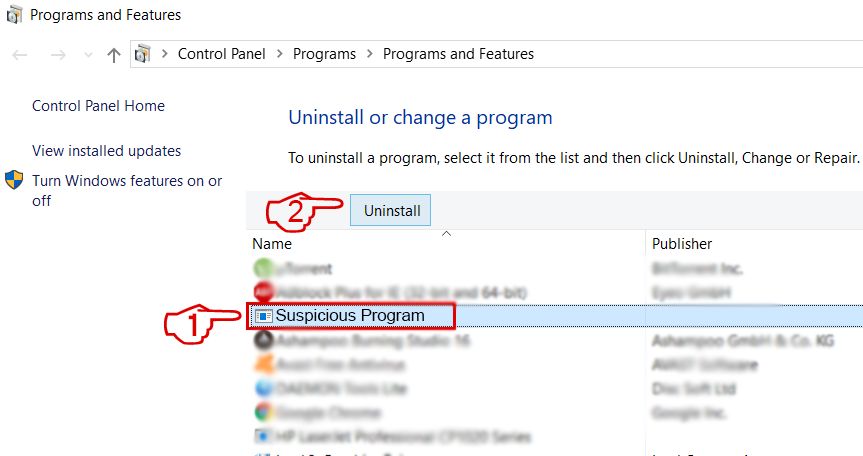 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
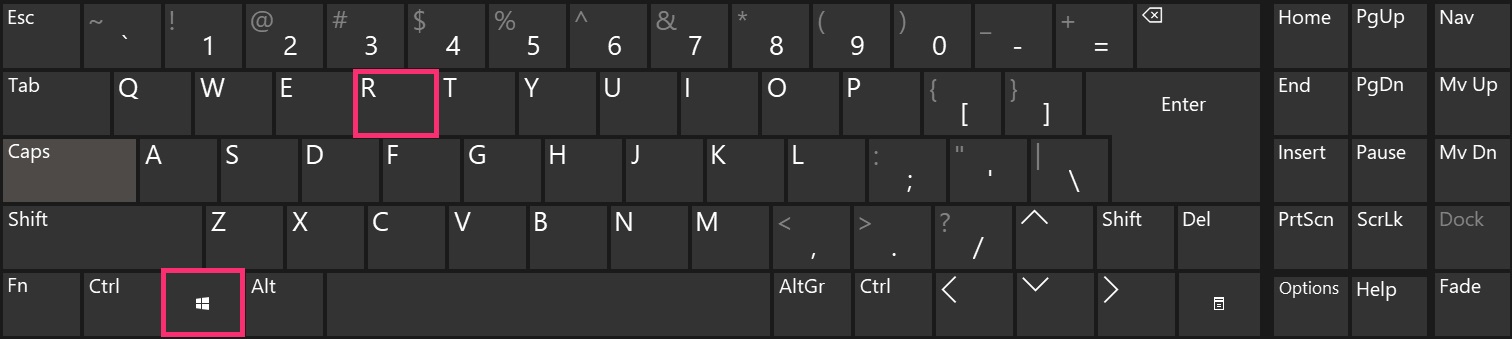
Step 3: Clean any registries, created by .corrupt Ransomware on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by .corrupt Ransomware there. This can happen by following the steps underneath:
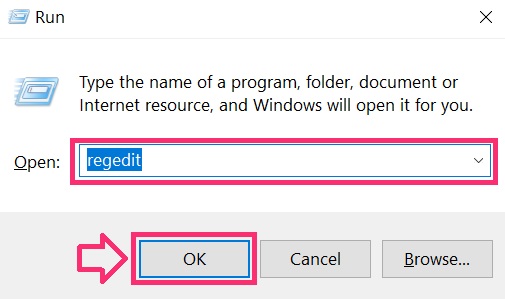
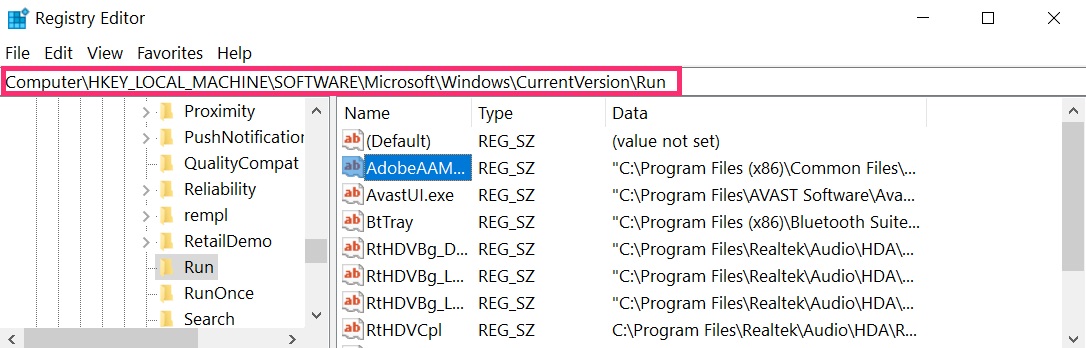
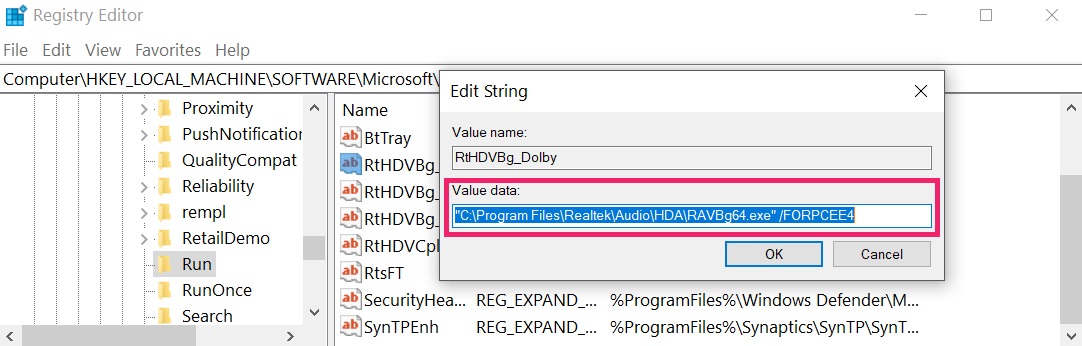 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
IMPORTANT!
Before starting "Step 4", please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
Step 4: Scan for .corrupt Ransomware with SpyHunter Anti-Malware Tool


Step 5 (Optional): Try to Restore Files Encrypted by .corrupt Ransomware.
Ransomware infections and .corrupt Ransomware aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested a data recovery method that may help you go around direct decryption and try to restore your files. Bear in mind that this method may not be 100% effective but may also help you a little or a lot in different situations.
Simply click on the link and on the website menus on top, choose Data Recovery - Data Recovery Wizard for Windows or Mac (depending on your OS), and then download and run the tool.
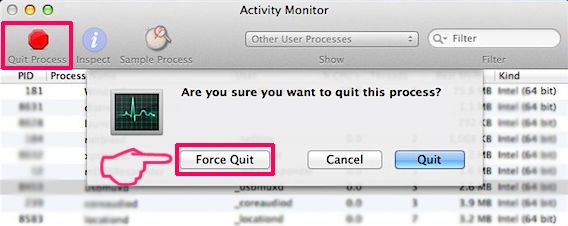
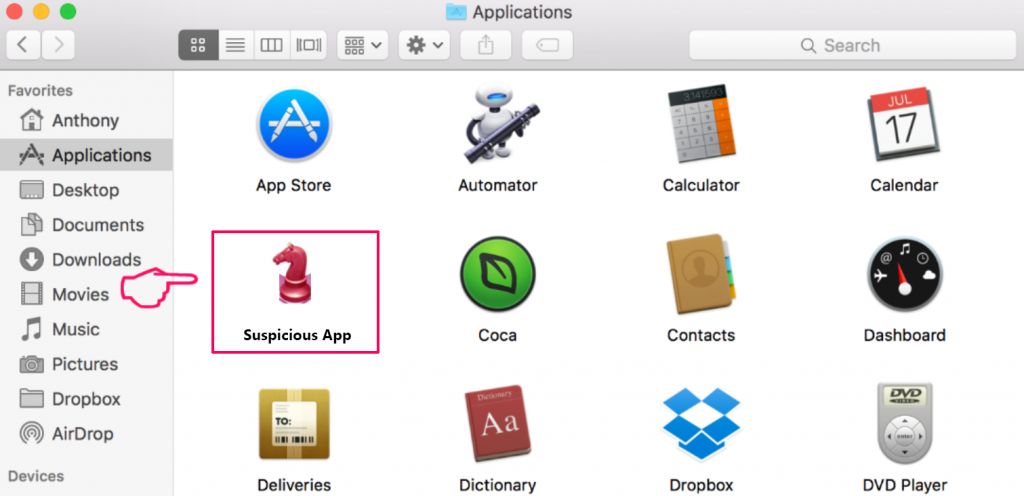
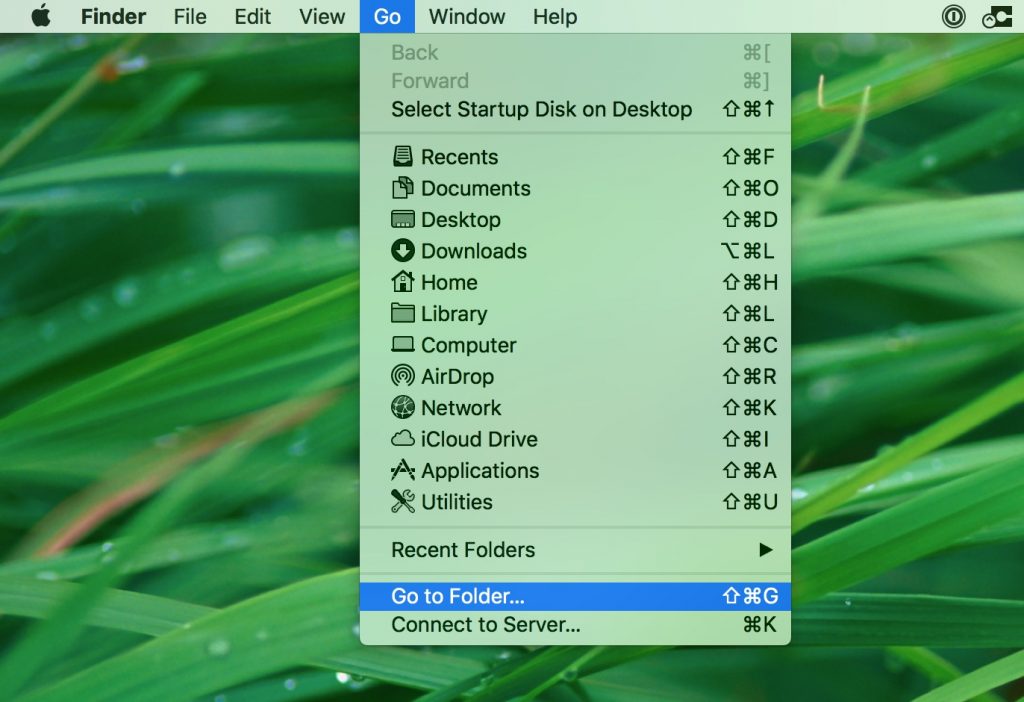
Step 1: Uninstall .corrupt Ransomware and remove related files and objects In case you cannot remove .corrupt Ransomware via Step 1 above: In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below: Disclaimer! If you are about to tamper with Library files on Mac, be sure to know the name of the virus file, because if you delete the wrong file, it may cause irreversible damage to your MacOS. Continue on your own responsibility! You can repeat the same procedure with the following other Library directories: → ~/Library/LaunchAgents Tip: ~ is there on purpose, because it leads to more LaunchAgents. Download SpyHunter for Mac Step 3 (Optional): Try to Restore Files Encrypted by .corrupt Ransomware. Ransomware infections and .corrupt Ransomware aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested a data recovery method that may help you go around direct decryption and try to restore your files. Bear in mind that this method may not be 100% effective but may also help you a little or a lot in different situations. Simply click on the link and on the website menus on top, choose Data Recovery - Data Recovery Wizard for Windows or Mac (depending on your OS), and then download and run the tool. .corrupt Ransomware is a ransomware infection - the malicious software that enters your computer silently and blocks either access to the computer itself or encrypt your files. Many ransomware viruses use sophisticated encryption algorithm how to make your files inaccessible. The goal of ransomware infections is to demand that you pay a ransom payment to get access to your files back. Via several ways..corrupt Ransomware Ransomware infects computers by being sent via phishing e-mails, containing virus attachment. This attachment is usually masked as an important document, like an invoice, bank document or even a plane ticket and it looks very convincing to users. After you download and execute this attachment, a drive-by download occurs and your computer is infected with the ransomware virus. Another way, you may become a victim of .corrupt Ransomware is if you download a fake installer, crack or patch from a low reputation website or if you click on a virus link. Many users report getting a ransomware infection by downloading torrents. You can't. At this point the ..corrupt Ransomware files are encrypted. You can only open them once they are decrypted. Do not panic and backup the files. If a decryptor did not decrypt your ..corrupt Ransomware files successfully, then do not despair, because this virus is still new. One way to restore files, encrypted by .corrupt Ransomware ransomware is to use a decryptor for it. But since it's a new virus, advised that the decryption keys for it may not be out yet and available to the public. We will update this article and keep you posted as soon as this decryptor is released. Yes, sometimes files can be restored. We have suggested several file recovery methods that could work if you want to restore ..corrupt Ransomware files. These methods are in no way 100% guarantee that you will be able to get your files back. But if you have a backup, your chances of success are much greater. The safest way and the most efficient one for the removal of this ransomware infection is the use a professional anti malware software. It will scan for and locate .corrupt Ransomware ransomware and then remove it without causing any additional harm to your important ..corrupt Ransomware files. Also, keep in mind that viruses like .corrupt Ransomware ransomware also install Trojans and keyloggers that can steal your passwords and accounts. Scanning your computer with an anti-malware software will make sure that all of these virus components are removed and your computer is protected in the future. There is still a lot you can do. If none of the above methods seem to work for you, then try these methods: More tips you can find on our forums, where you can also asks any questions about your ransomware problem.
Windows Mac OS X
Get rid of .corrupt Ransomware from Mac OS X.
1. Hit the ⇧+⌘+U keys to open Utilities. Another way is to click on "Go" and then click "Utilities", like the image below shows: 


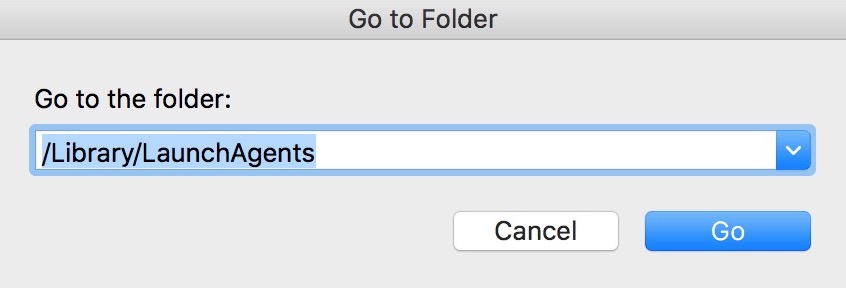
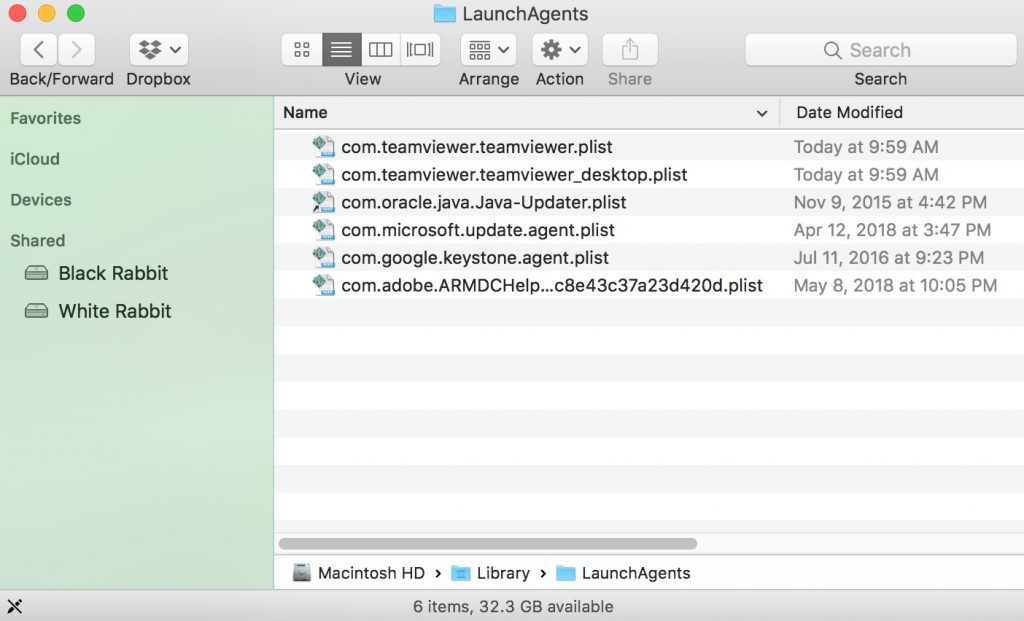
/Library/LaunchDaemons
.corrupt Ransomware FAQ
What is .corrupt Ransomware ransomware and how does it work?
How does .corrupt Ransomware ransomware infect my computer?
How to open ..corrupt Ransomware files?
Decryptor did not decrypt my data. What now?
How Do I restore "..corrupt Ransomware" files (Other Methods)?
How do I get rid of .corrupt Ransomware ransomware virus?
What to Do If nothing works?
How to Report Ransomware to Authorities?
Source: https://sensorstechforum.com/corrupt-files-virus-remove-restore-encrypted-documents/

0 Response to "Laptop Virus Enccrypted Files Blue Screen Pc Needs Repair"
Publicar un comentario